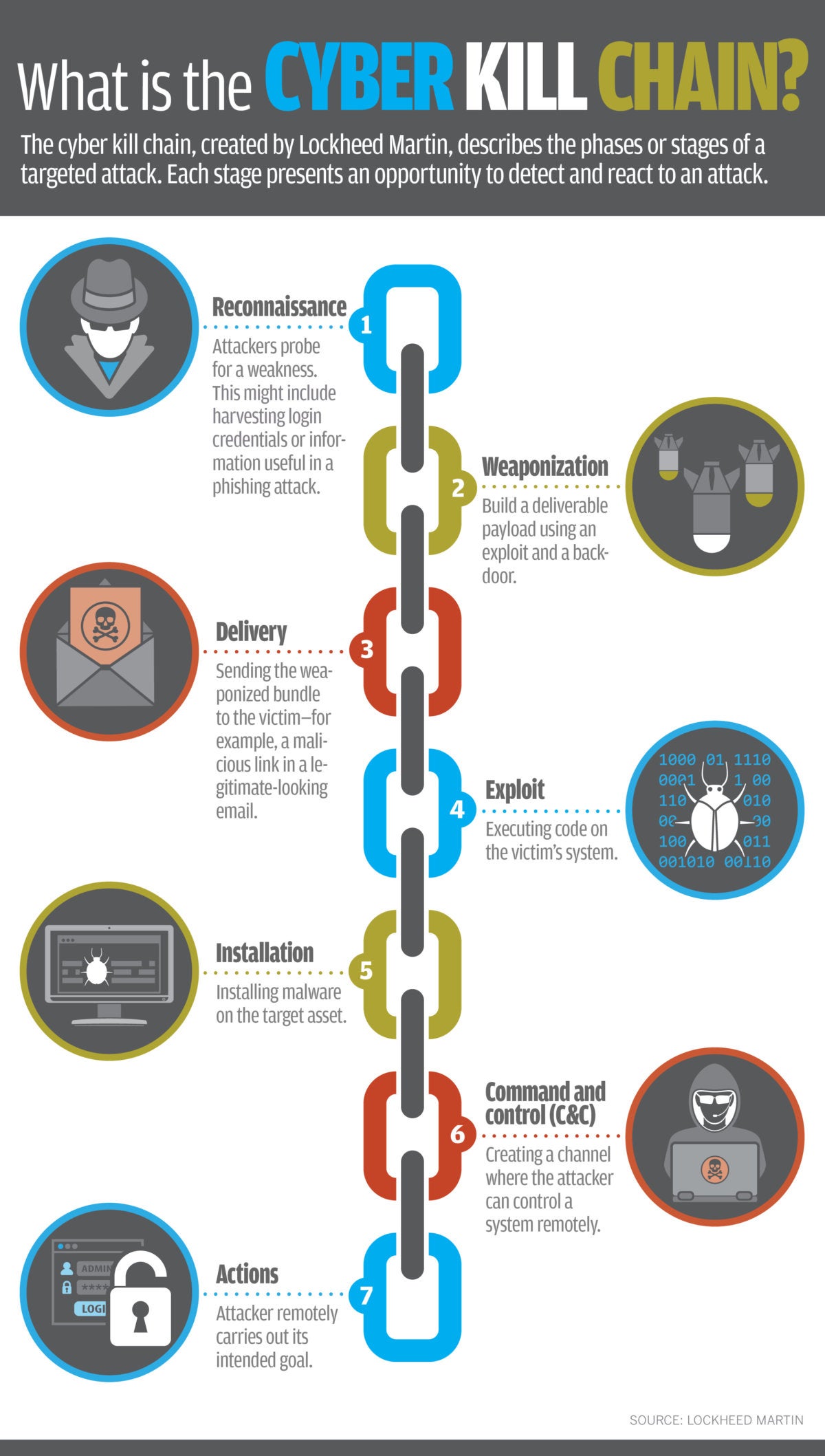
Is the Cyber Kill Chain Model the Ultimate Solution to Rising Ransomware Attacks? - United States Cybersecurity Magazine

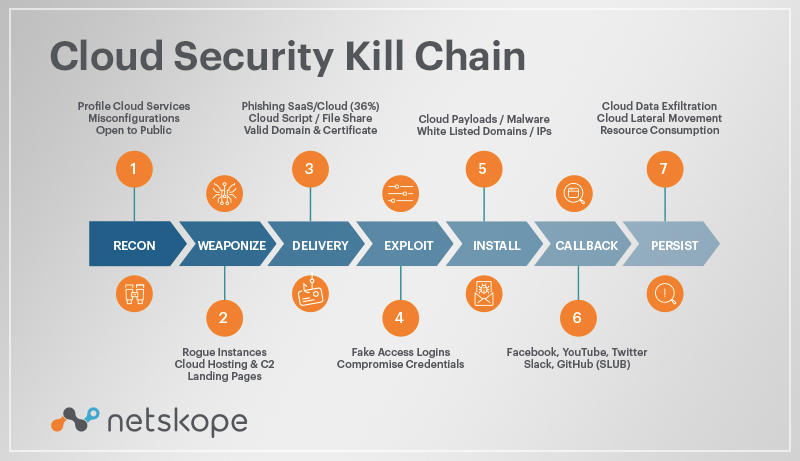
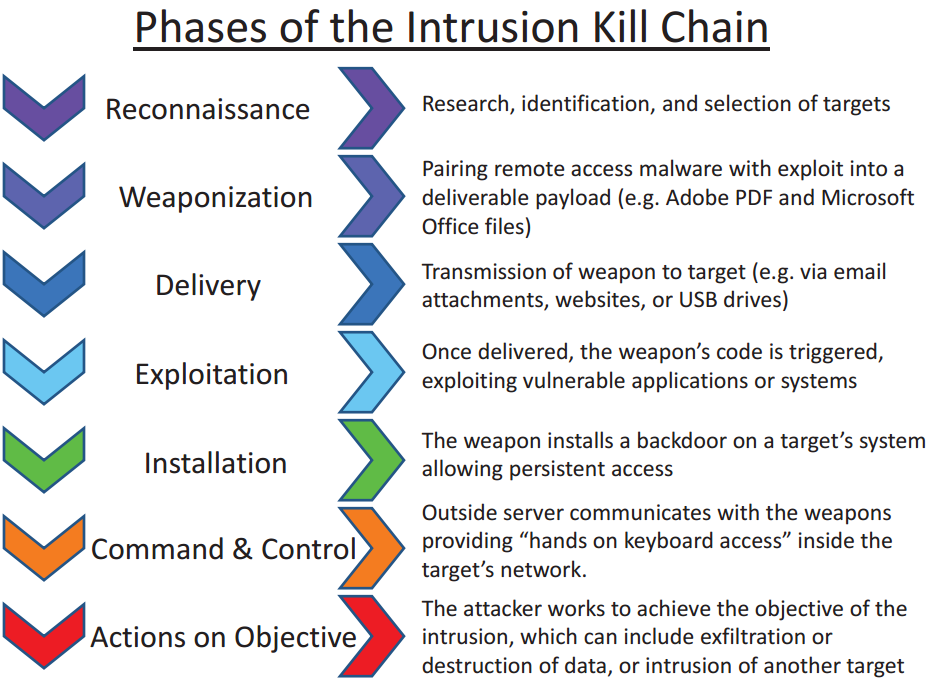
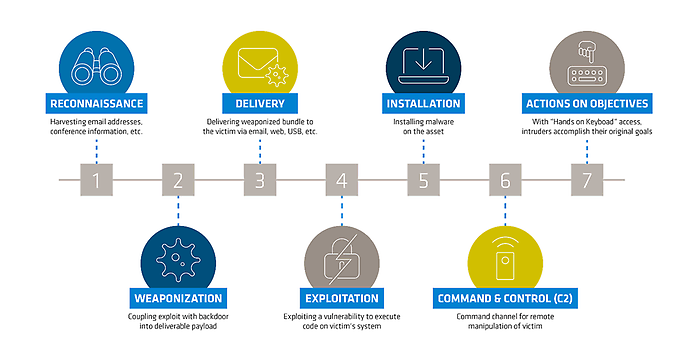
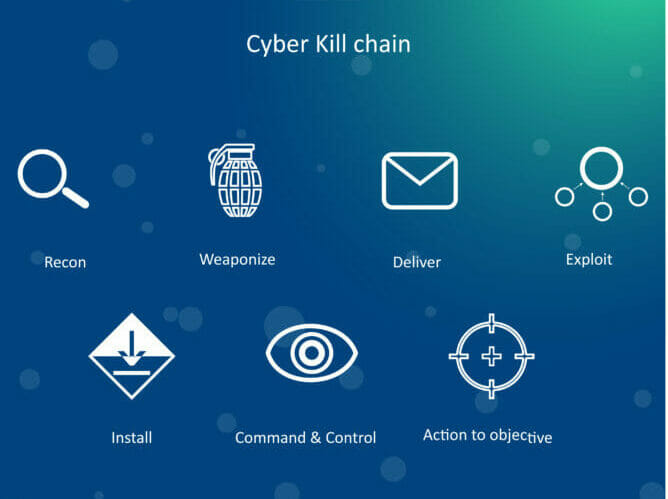
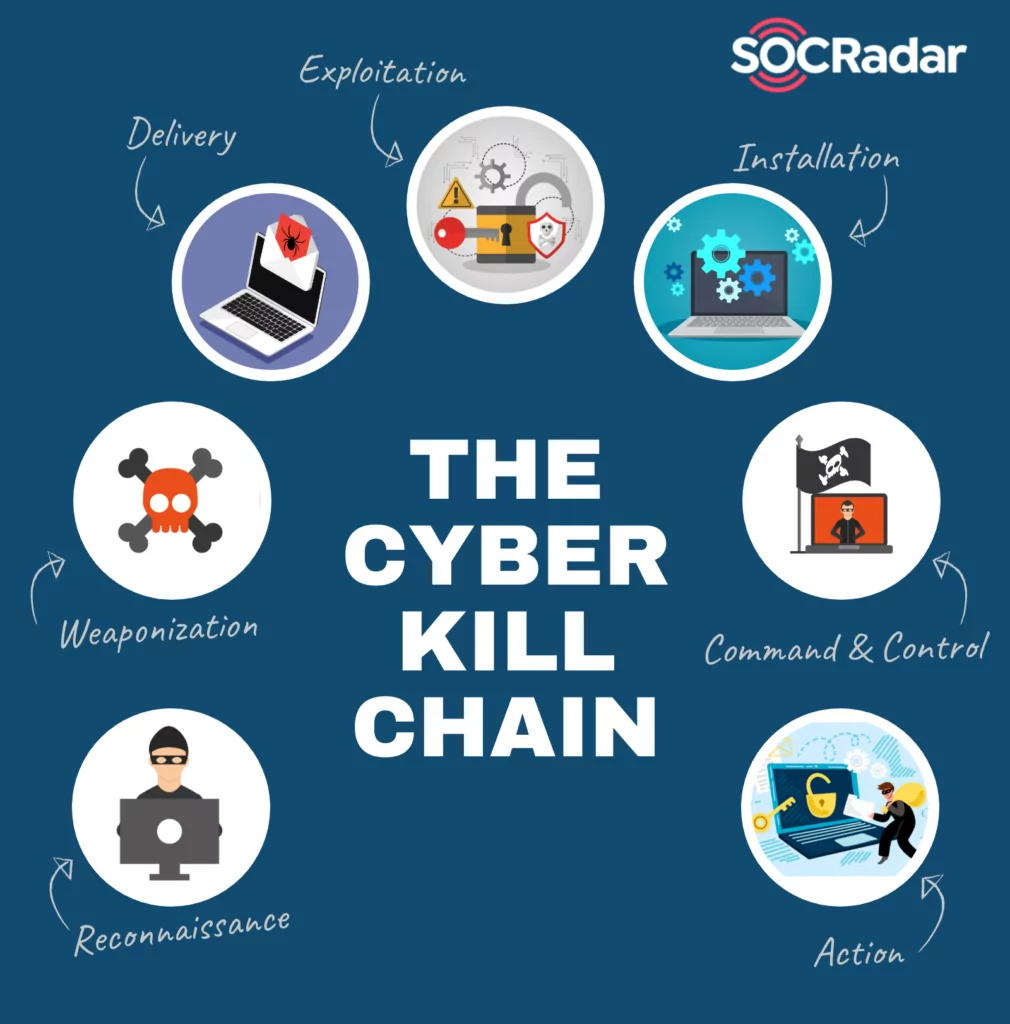
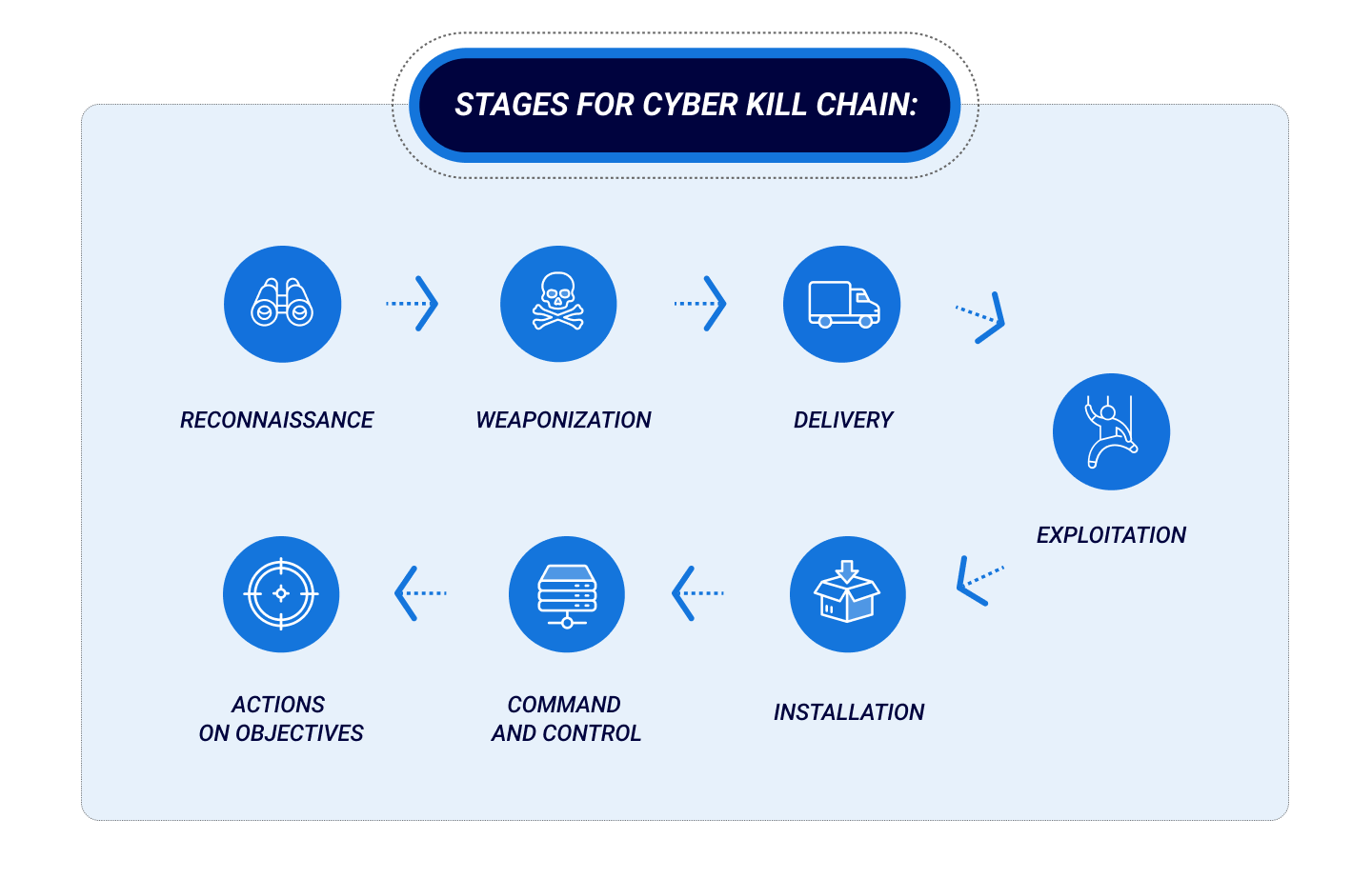
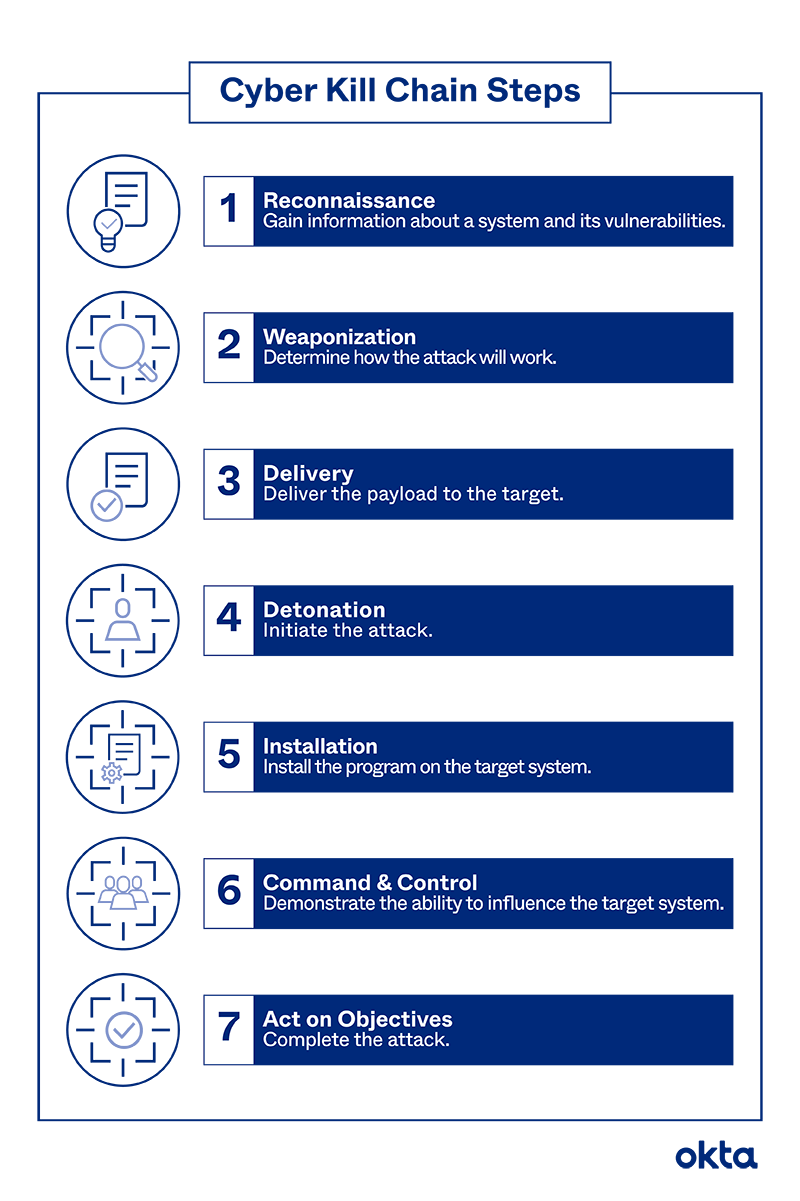
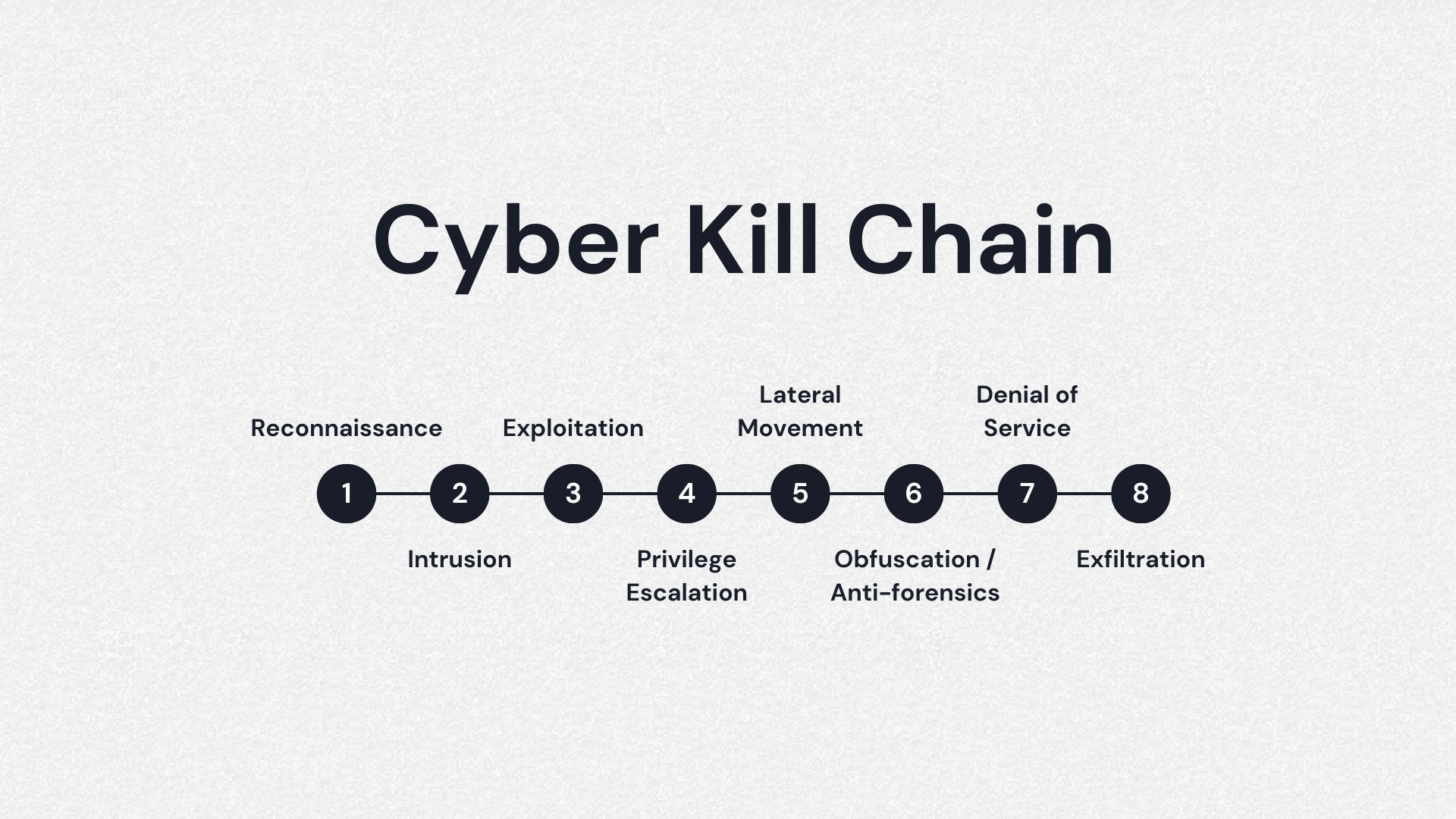
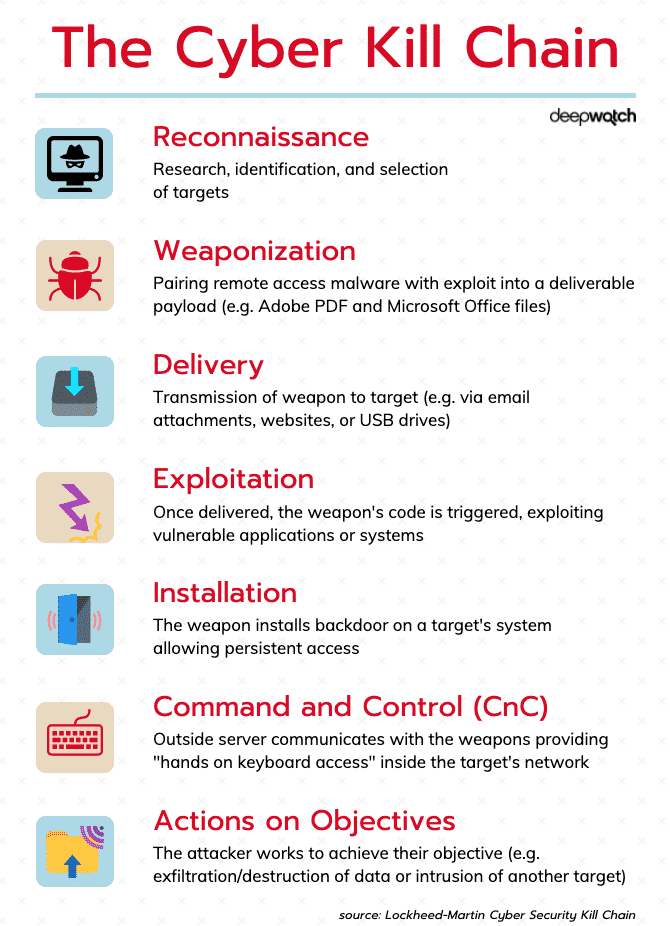
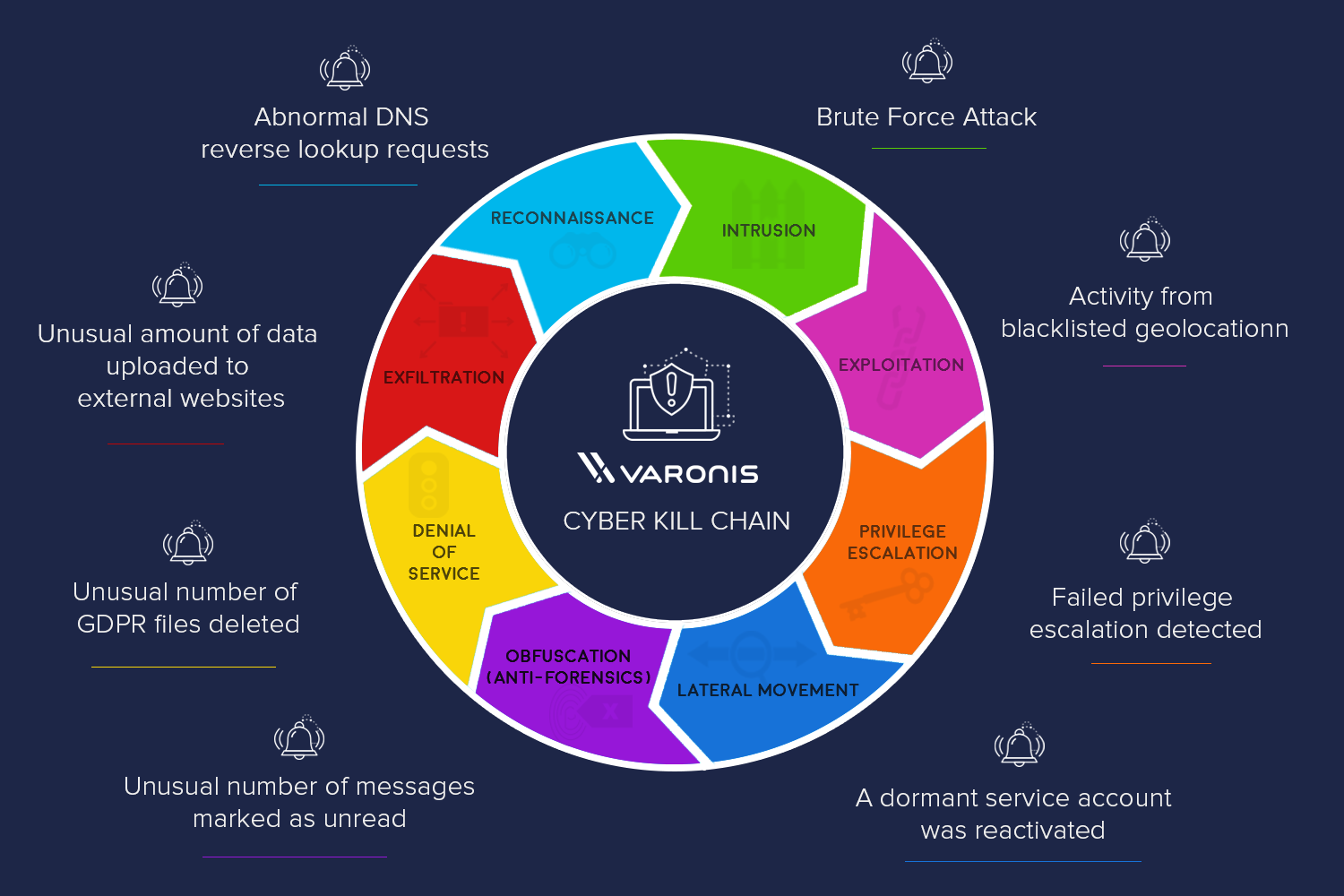
EC-Council - The cyber kill chain helps prepare the organization for all common threats such as network breaches, data thefts, ransomware attacks, and advanced persistent attacks. Let's read more about the cyber